

Which two services define cloud networks? (Choose two.)
Correct Answer:
AB
🗳️
The diagram below depicts the Cloud Computing stack it shows three distinct categories within Cloud Computing: Software as a Service, Platform as a Service and Infrastructure as a Service.
A simplified way of differentiating these flavors of Cloud Computing is as follows;
✑ SaaS applications are designed for end-users, delivered over the web
✑ PaaS is the set of tools and services designed to make coding and deploying those applications quick and efficient
✑ IaaS is the hardware and software that powers it all servers, storage, networks, operating systems
Reference: https://support.rackspace.com/white-paper/understanding-the-cloud-computing-stack-saas-paas-iaas/
In which two situations should you use out-of-band management? (Choose two.)
Correct Answer:
AB
🗳️
Out-of-band refers to an interface that allows only management protocol traffic to be forwarded or processed. An out-of-band management interface is defined by the network operator to specifically receive network management traffic. The advantage isthat forwarding (or customer) traffic cannot interfere with the management of the router, which significantly reduces the possibility of denial-of-service attacks.
Out-of-band interfaces forward traffic only between out-of-band interfaces or terminate management packets that are destined to the router. In addition, the out-of- band interfaces can participate in dynamic routing protocols. The service provider connects to the routers out-of-band interfaces and builds an independent overlay management network, with all the routing and policy tools that the router can provide.
Reference: http://www.cisco.com/c/en/us/td/docs/routers/asr9000/software/asr9k_r4-0/security/configuration/guide/b_sc40asr9kbook/ b_sc40asr9kbook_chapter_0101.pdf
In which three ways does the TACACS protocol differ from RADIUS? (Choose three.)
Correct Answer:
ABC
🗳️
TACACS+ uses Transmission Control Protocol (TCP) port 49 to communicate between the TACACS+ client and the TACACS+ server. An example is a Cisco switch authenticating and authorizing administrative access to the switchs IOS CLI. The switch is the TACACS+ client, and Cisco Secure ACS is the server.
TACACS+ communication between the client and server uses different message types depending on the function. In other words, different messages may be used for authentication than are used for authorization and accounting. Another very interesting point to know is that TACACS+ communication will encrypt the entire packet.
Reference: http://www.networkworld.com/article/2838882/radius-versus-tacacs.html
According to Cisco best practices, which three protocols should the default ACL allow on an access port to enable wired BYOD devices to supply valid credentials and connect to the network? (Choose three.)
Correct Answer:
ABC
🗳️
ACL-DEFAULT allows DHCP, DNS, ICMP, and TFTP traffic and denies everything else.
Reference: http://www.cisco.com/c/en/us/td/docs/solutions/Enterprise/Borderless_Networks/Unified_Access/BYOD_Design_Guide/BYOD_Wired.html
Which two next-generation encryption algorithms does Cisco recommend? (Choose two.)
Correct Answer:
Answer: A, F
🗳️
The following table shows the relative security level provided by the recommended and NGE algorithms. The security level is the relative strength of an algorithm. bits, the relative effort it would take to "beat"
-bit symmetric key algorithm (without reduction or other attacks). The 128-bit security level is for sensitive information and the 192-bit level is for information of higher importance.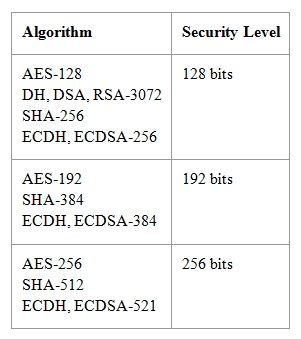
Reference:
http://www.cisco.com/c/en/us/about/security-center/next-generation-cryptography.html
Which three ESP fields can be encrypted during transmission? (Choose three.)
Correct Answer:
DEF
🗳️
The remaining four parts of the ESP are all encrypted during transmission across the network. Those parts are as follows:
✑ is the actual data that is carried by the packet.
✑ , from 0 to 255 bytes of data, allows certain types of encryption algorithms to require the data to be a multiple of a certain number of bytes. The padding also ensures that the text of a message terminates ona four-byte boundary (an architectural requirement within IP).
✑ field specifies how much of the payload is padding rather than data.
✑ field, identifies the type of data carried and the protocol.
Reference:
http://www.cisco.com/c/en/us/td/docs/net_mgmt/vpn_solutions_center/2-0/ip_security/provisioning/guide/IPsecPG1.html
What are two default Cisco IOS privilege levels? (Choose two.)
Correct Answer:
BF
🗳️
By default, the Cisco IOS software command-line interface (CLI) has two levels of access to commands: user EXEC mode (level 1) and privileged EXEC mode
(level 15). However, you can configure additional levels of access to commands, called privilege levels, to meet the needs of your users while protecting the system from unauthorized access. Up to 16 privilege levels can be configured, from level 0, which is the most restricted level, to level 15, which is the least restricted level.
Reference:
http://www.cisco.com/c/en/us/td/docs/ios/12_2/security/configuration/guide/fsecur_c/scfpass.html#wp1001016
Which two authentication types does OSPF support? (Choose two.)
Correct Answer:
AB
🗳️
These are the three different types of authentication supported by OSPF.
✑ Null AuthenticationThis is also called Type 0 and it means no authentication information is included in the packet header. It is the default.
✑ Plain Text AuthenticationThis is also called Type 1 and it uses simple clear-text passwords.
✑ MD5 AuthenticationThis is also called Type 2 and it uses MD5 cryptographic passwords.
Authentication does not need to be set. However, if it is set, all peer routers on the same segment must have the same password and authentication method. The examples in this document demonstrate configurations for both plain text and MD5 authentication.
Reference:
http://www.cisco.com/c/en/us/support/docs/ip/open-shortest-path-first-ospf/13697-25.html
Which two features do CoPP and CPPr use to protect the control plane? (Choose two.)
Correct Answer:
AB
🗳️
Which two statements about stateless firewalls are true? (Choose two.)
Correct Answer:
AB
🗳️
However, since iptables and Netfilter were introduced and connection tracking in particular, this option was gotten rid of. The reason for this is that connection tracking can not work properly without defragmenting packets, and hence defragmenting has been incorporated into conntrack and is carried out automatically. It can not be turned off, except by turning off connection tracking. Defragmentation is always carried out if connection tracking is turned on.
Reference:
http://www.iptables.info/en/connection-state.html