

You want to gather as much detail as possible during a network audit, to include data time stamping across a large number of interfaces, customized according to interface, with a minimal impact on the network devices themselves. Which tool would you use to meet these requirements?
Correct Answer:
C
🗳️
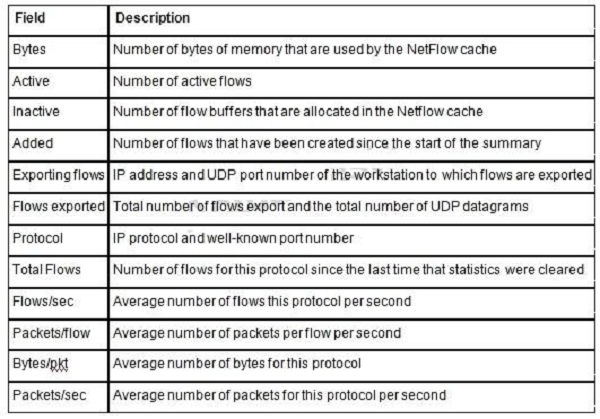
NetFlow provides extremely granular and accurate traffic measurements and a high-level collection of aggregated traffic. The output of netflow information is displayed via the show ip cache flow command on routers. The Table shows a description of the fields for NetFlow output.
Table. Netflow Output escription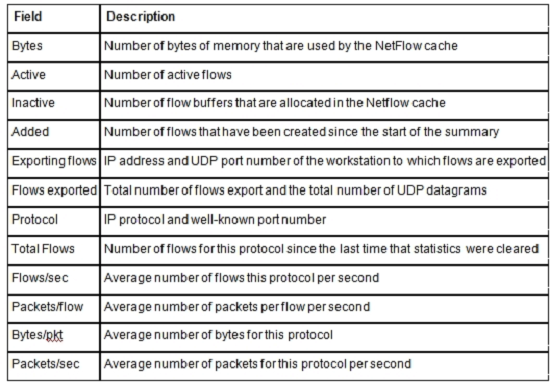
You want to gather as much detail as possible during a network audit with a minimal impact on the network devices themselves. Which tool would you use to include data time stamping across a large number of interfaces while being customized according to each interface?
Correct Answer:
C
🗳️
In which phase of PPDIOO are the network requirements identified?
Correct Answer:
B
🗳️
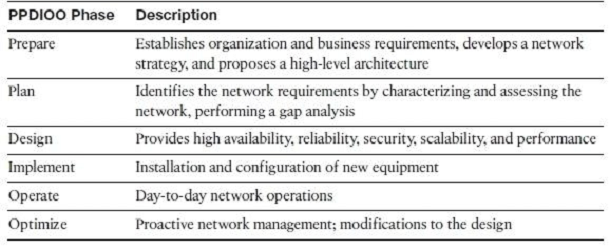
Plan Phase -
The Plan phase identifies the network requirements based on goals, facilities, and user needs. This phase characterizes sites and assesses the network, performs a gap analysis against best-practice architectures, and looks at the operational environment. A project plan is developed to manage the tasks, responsible parties, milestones, and resources to do the design and implementation. The project plan aligns with the scope, cost, and resource parameters established with the original business requirements. This project plan is followed (and updated) during all phases of the cycle.
Which is part of the Prepare phase of PPDIOO?
Correct Answer:
C
🗳️
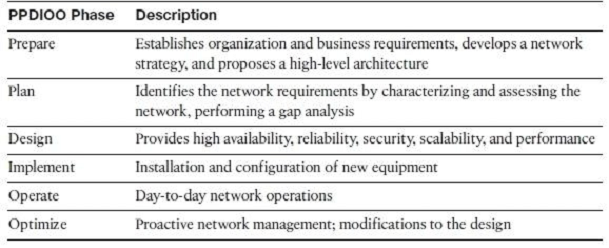
Prepare Phase -
The Prepare phase establishes organization and business requirements, develops a network strategy, and proposes a high-level conceptual architecture to support the strategy. Technologies that support the architecture are identified. This phase creates a business case to establish a financial justification for a network strategy.
When designing the identity and access control portions for the enterprise campus network, which of these solutions would be the most appropriate solution to consider?
Correct Answer:
A
🗳️
Which is the purpose of the Cisco NAC Profiler?
Correct Answer:
A
🗳️
Cisco NAC Profiler: Enables network administrators to keep a real-time, contextual inventory of all devices in a network. It greatly facilitates the deployment and management of Cisco Network Admission Control (NAC) systems by discovering and tracking the location and type of all LAN-attached endpoints, including those that are not capable of authenticating. It also uses the information about the device to determine the correct policies for NAC to apply.
Cisco Identity-Based Networking Services relies heavily on the 802.1X protocol. Which other authentication solution is used hand-in-hand with 802.1X to authenticate users for network access?
Correct Answer:
A
🗳️
Cisco Identity-Based Network Services
The Cisco Identity-Based Network Services solution is a way to authenticate host access based on policy for admission to the network. IBNS supports identity authentication, dynamic provisioning of VLANs on a per-user basis, guest VLANs, and 802.1X with port security.
The 802.1 X protocol is a standards-based protocol for authenticating network clients by permitting or denying access to the network. The 802.1 X protocol operates between the end-user client seeking access and an Ethernet switch or wireless access point (AP) providing the connection to the network. In 802.1 X terminology, clients are called supplicants, and switches and APs are called authenticates. A back-end RADIUS server such as a Cisco Access Control Server
(ACS) provides the user account database used to apply authentication and authorization.
With an IBNS solution, the host uses 802.IX and Extensible Authentication Protocol over LANs (EAPoL) to send the credentials and initiate a session to the network. After the host and switch establish LAN connectivity, username and password credentials are requested. The client host then sends the credentials to the switch, which forwards them to the RADIUS ACS.
The RADIUS ACS performs a lookup on the username and password to determine the credentials' validity. If the username and password are correct, an accept message is sent to the switch or AP to allow access to the client host. If the username and password are incorrect, the server sends a message to the switch or
AP to block the host port.
Figure 13-4 illustrates the communication flow of two hosts using 802.1X and KAPoL with the switch, AP, and back-end RADIUS server.
Which protocol is used for voice bearer traffic?
Correct Answer:
B
🗳️
VoIP Control and Transport Protocols
A number of different protocols are used in a VoIP environment for call control, device provisioning, and addressing.
Figure 14-15 shows those protocols focused on VoIP control and transport.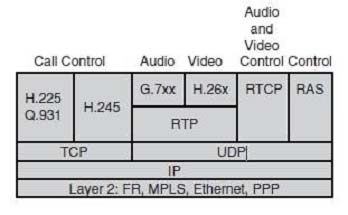
Which protocol is used to reserve bandwidth for the transport of a particular application data flow across the network?
Correct Answer:
C
🗳️
RSVP Signaling protocol that enables end stations or applications to obtain guaranteed bandwidth and low delays for their data flows.
Which two features are supported by single wireless controller deployments? (Choose two.)
Correct Answer:
AB
🗳️