

Suppose that you test an application for the SQL injection vulnerability. You know that the backend database is based on Microsoft SQL Server. In the login/ password form, you enter the following credentials: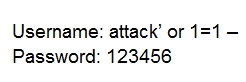
Based on the above credentials, which of the following SQL commands are you expecting to be executed by the server, if there is indeed an SQL injection vulnerability?
Daniel8660
Highly Voted 1 year agovictorfs
Most Recent 5 months, 3 weeks agoVOAKDO
9 months, 2 weeks agojosevirtual
11 months, 1 week agokiki533
12 months agoC1ph3rSt0rm
1 year agokiki533
12 months agoAaronS1990
10 months, 4 weeks agoShashika90
1 year, 1 month agosn30
1 year, 1 month agonapstervk
1 year, 1 month agoEscltn
1 year, 1 month agoEscltn
1 year, 1 month agoflinux
1 year, 1 month ago