

HOTSPOT -
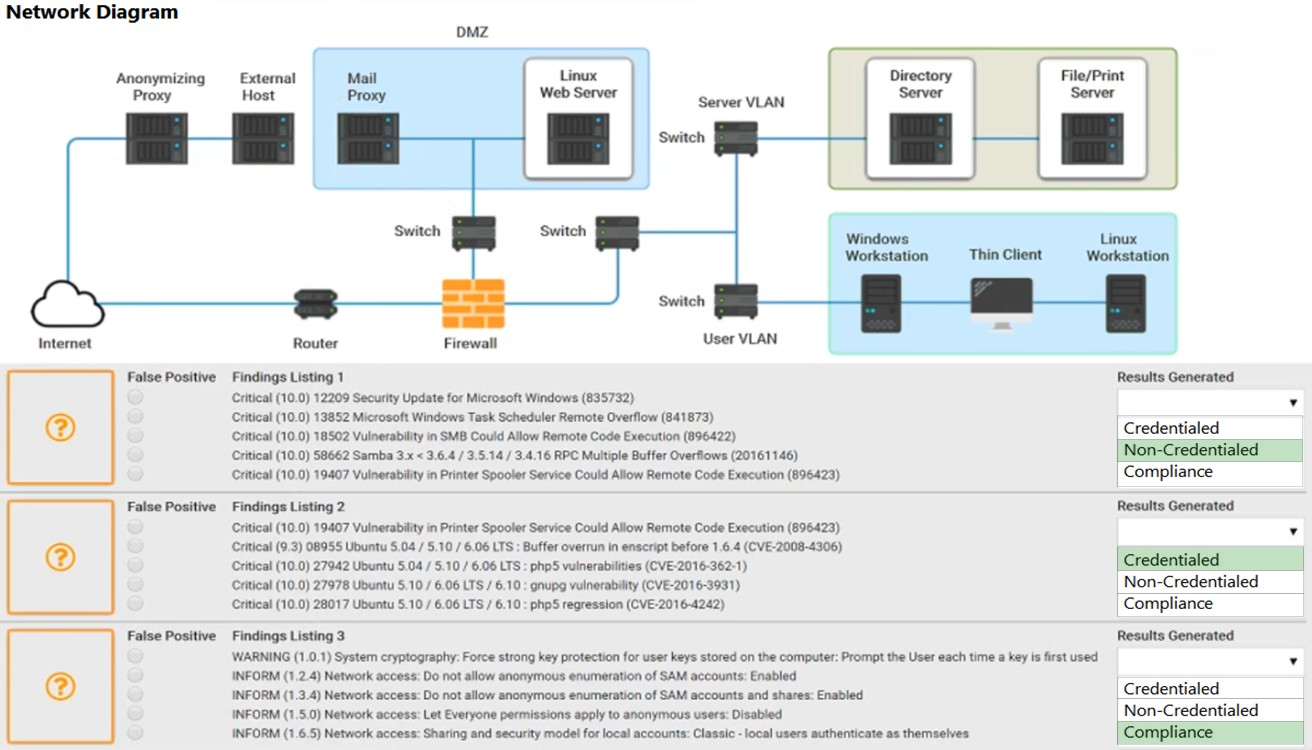
A security analyst performs various types of vulnerability scans.
Review the vulnerability scan results to determine the type of scan that was executed and if a false positive occurred for each device.
INSTRUCTIONS -
Select the Results Generated drop-down option to determine if the results were generated from a credentialed scan, non-credentialed scan, or a compliance scan.
For ONLY the credentialed and non-credentialed scans, evaluate the results for False Positives and check the Findings that display false positives.
NOTE: If you would like to uncheck an option that is currently selected, click on the option a second time.
Lastly, based on the vulnerability scan results, identify the type of Server by dragging the Server to the results. The Linux Web Server, File-Print Server, and
Directory Server are draggable.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
Hot Area: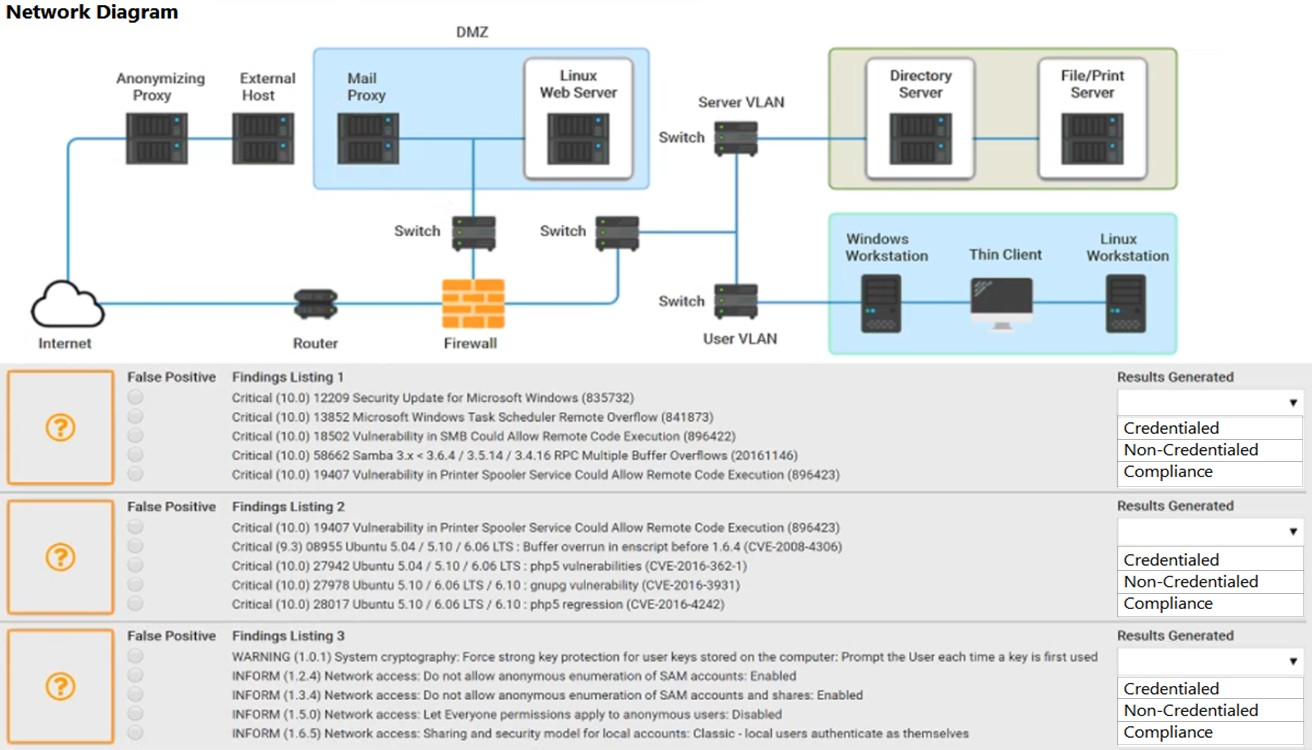
db97
Highly Voted 2 years, 2 months agokhrid4
2 years agoZUL01
1 year, 11 months agodb97
2 years, 2 months agomraval
2 years, 1 month agoWeezyfbaby
Highly Voted 2 years, 6 months agoSolventCourseisSCAM
2 years, 5 months agoStarburst
Most Recent 1 year, 9 months agoZUL01
1 year, 11 months agodb97
2 years, 2 months agoZUL01
1 year, 11 months agodavid124
2 years, 2 months agoJoshgip95
2 years, 1 month agoIanRogerStewart
2 years, 2 months agocatastrophie
2 years, 2 months agoSylFlo
2 years, 2 months agoSOL_Z
2 years, 2 months agoMrRobotJ
2 years, 5 months agolordguck
2 years, 4 months agoVanicream
2 years, 5 months agodb97
2 years, 2 months agomandimus
2 years, 5 months agoJoshgip95
2 years, 1 month agojchutch2
2 years, 6 months agoR00ted
2 years, 7 months agojchutch2
2 years, 6 months agoR00ted
2 years, 6 months agodb97
2 years, 2 months agocatastrophie
2 years, 2 months ago2Fish
2 years, 1 month ago2Fish
2 years agoLaudy
2 years, 7 months ago